Take control of your data. Learn how to set up a private Matrix server with Conduit or Synapse, configure bridges for Telegram/WhatsApp, and ensure E2EE privacy.
Master privacy with local LLMs. Learn to encrypt data, use AI steganography, and prevent leaks by running models offline. Essential guide for digital sovereignty.
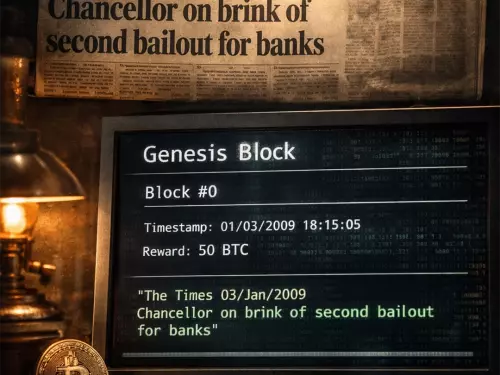
Discover why Bitcoin is a strategic experiment for modeling digital behavior and how its data paved the legal and technical way for the rise of CBDCs.
Explore the intelligence agency hypothesis behind Bitcoin's creation. Analyze how the 2008 financial crisis and national security led to Satoshi Nakamoto's experiment.
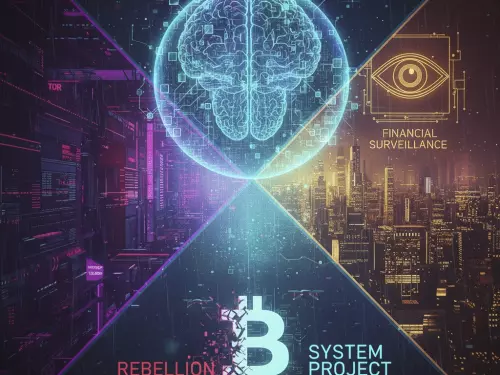
Is Bitcoin a rebel tool or a state project? Compare Bitcoin to TOR and discover why its permanent ledger might be a dream for financial intelligence agencies.
Who is Satoshi Nakamoto? Explore how Cypherpunks like Adam Back, Wei Dai, and Nick Szabo shaped Bitcoin’s DNA through Hashcash, b-money, and Bit Gold.
The ultimate guide to Zero-Knowledge Proofs (ZKPs): See how Zcash, Firo, and Aleo hide sender, receiver, and amount. SNARKs vs. STARKs explained for blockchain privacy.
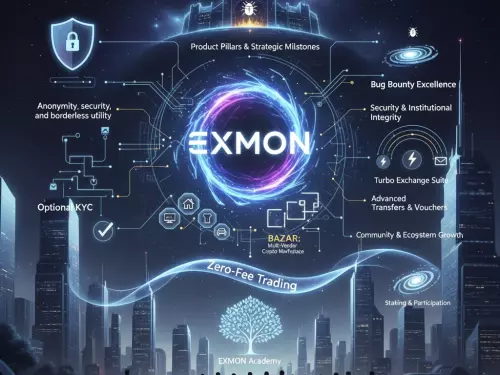
From Mt. Gox chaos to Coinbase compliance and EXMON's user sovereignty. Explore the decade-long story of crypto trading's evolution, security failures, and the platforms building the future of finance.