Stop copy-pasting AI configs. We dive into the critical flaws in ChatGPT's logic that expose your IP and kill your node's anonymity. Stay dark, stay safe.
Build an autonomous Raspberry Pi node for mixer operations. Learn to implement physical self-destruct keys, LUKS detached headers, and anti-forensics in 2026.
How Canvas & WebGL rendering de-anonymize crypto wallets even with a VPN. Learn professional tactics to block browser tracking and secure your digital identity.
Explore how ZK-proofs, biometrics, and social graphs verify humanity in 2026. Practical guide to PoP protocols, UBI economy, and fighting AI deepfakes.
Inside the Hinkal Protocol: How Vitalik Buterin’s "Invisible Wallets" and ZK-proofs are enabling Fortune 500 firms to shield corporate funds from public view.
Master the mechanics of crypto dusting attacks. Learn how funds and agencies link UTXOs to track your identity and how to defend your privacy using Coin Control.
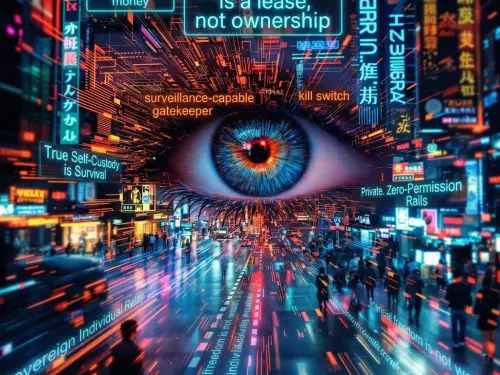
Discover why the traditional financial system is a "permissioned life." Explore the truth about CBDCs, the failure of crypto, and how to reclaim autonomy.
Take control of your data. Learn how to set up a private Matrix server with Conduit or Synapse, configure bridges for Telegram/WhatsApp, and ensure E2EE privacy.
Master privacy with local LLMs. Learn to encrypt data, use AI steganography, and prevent leaks by running models offline. Essential guide for digital sovereignty.
The truth about data storage on crypto exchanges in 2026. Real-world leaks, staff access to IDs, and the hidden risks of third-party KYC vendors. Read more!
How is crypto tracked? Learn how the FBI, DHS, Chainalysis, and Elliptic monitor transactions through exchanges. Full tracking schemes revealed. Read more!